Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
Barracuda Reputation Alert
Current Version
1.0
Last Release Date
2013-05-08
Compatible With
- Nagios 3.x
- Nagios 4.x
Owner
License
GPL
Hits
41254
Files:
| File | Description |
|---|---|
| cudacheck | cudacheck python script |
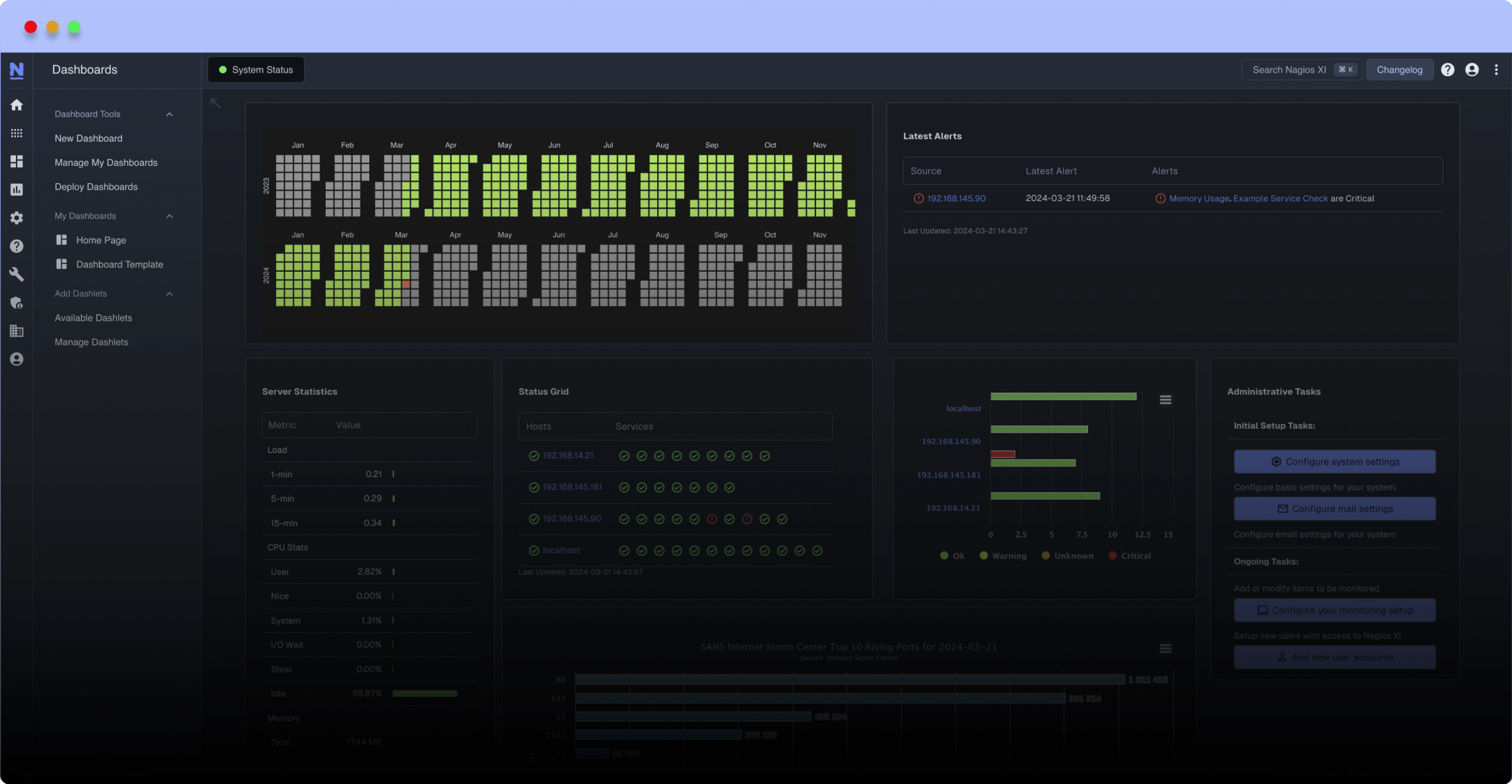
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
This script checks postfix log files for Barracuda reputation / RBL issues and alerts when found. Includes IP address in alert to simplify removal request process.
On occasion you may see false positives from Barracuda devices with an out of date RBL list.
**Written in Python 2.7.4 and currently in production on v2.7.4 and v2.6. No other versions of Python have been tested**
Place the 'cudacheck' file in /usr/lib(64)/nagios/plugins directory and ensure the permissions allow it to be executed. Add a command entry in /etc/nagios/nrpe.cfg to allow nagios to run the script with check_nrpe.
## define service on Nagios server ##
define service{
use linux-service
hosts
Place the 'cudacheck' file in /usr/lib(64)/nagios/plugins directory and ensure the permissions allow it to be executed. Add a command entry in /etc/nagios/nrpe.cfg to allow nagios to run the script with check_nrpe.
## define service on Nagios server ##
define service{
use linux-service
hosts
normal_check_interval 120
notification_interval 120
service_description Barracuda Reputation
check_command check_nrpe!check_cuda
}
There is no reason to run this check more often than the cutofftime set in the script. Ensure the normal_check_interval and notification_interval match the cutofftime. Default cutofftime is 2 hours. If you modified your default Nagios interval to something other than 60 seconds you'll need to account for that.
## SELinux Considerations ##
I have found two solutions for running this check with SELinux enabled:
1 - Permit the NRPE/Nagios user to execute the script with sudo rights
2 - Create a group for reading the mail logs, set the group and permissions on the log file and add the NRPE / Nagios user to the new group. The commands to complete these steps are below.
- groupadd newgroup
- usermod -a -G newgroup nrpe (or nagios depending on which user/group is set in your /etc/nagios/nrpe.conf)
- chown root.newgroup /var/log/maillog
- chmod 0640 /var/log/maillog
With option 2 you may need to write a script that monitors the permission and group settings of your log files and run it with a cronjob.
**EDIT**
The first version of this script included an error. The var "cutofftime" was originally called "twohoursago" and there were still references to that in the script. The current version of the file should not have this issue.
**NOTE**
This script only matches on your email logs for Barracuda Reputation alerts using a regex stringmatch. If you do not attempt delivery to a Barracuda device that rejects your email, it will not alert. This script does not perform lookups with Barracuda on your IPs, it is a mail log parsing script.
It is possible for a Barracuda device with an outdated blacklist to block your IP when you are not actively on the Barracuda blacklist. The only fix for this is for that recipient domain to white list you or to update their device.
Reviews (1)
bylibyanspider, April 4, 2014
receive back all status ok, even for IP with poor reputation if we check directly from http://www.barracudacentral.org/lookups/lookup-reputation
Barracuda Reputation - OK
Barracuda Reputation - OK
Owner's reply
It is possible for a device to report "poor" while Barracuda reports "ok", if the device in question has an outdated list.


 New Listings
New Listings