Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
check_yum
Current Version
1.1.0
Last Release Date
2014-09-26
Compatible With
- Nagios 3.x
Owner
License
GPL
Hits
262536
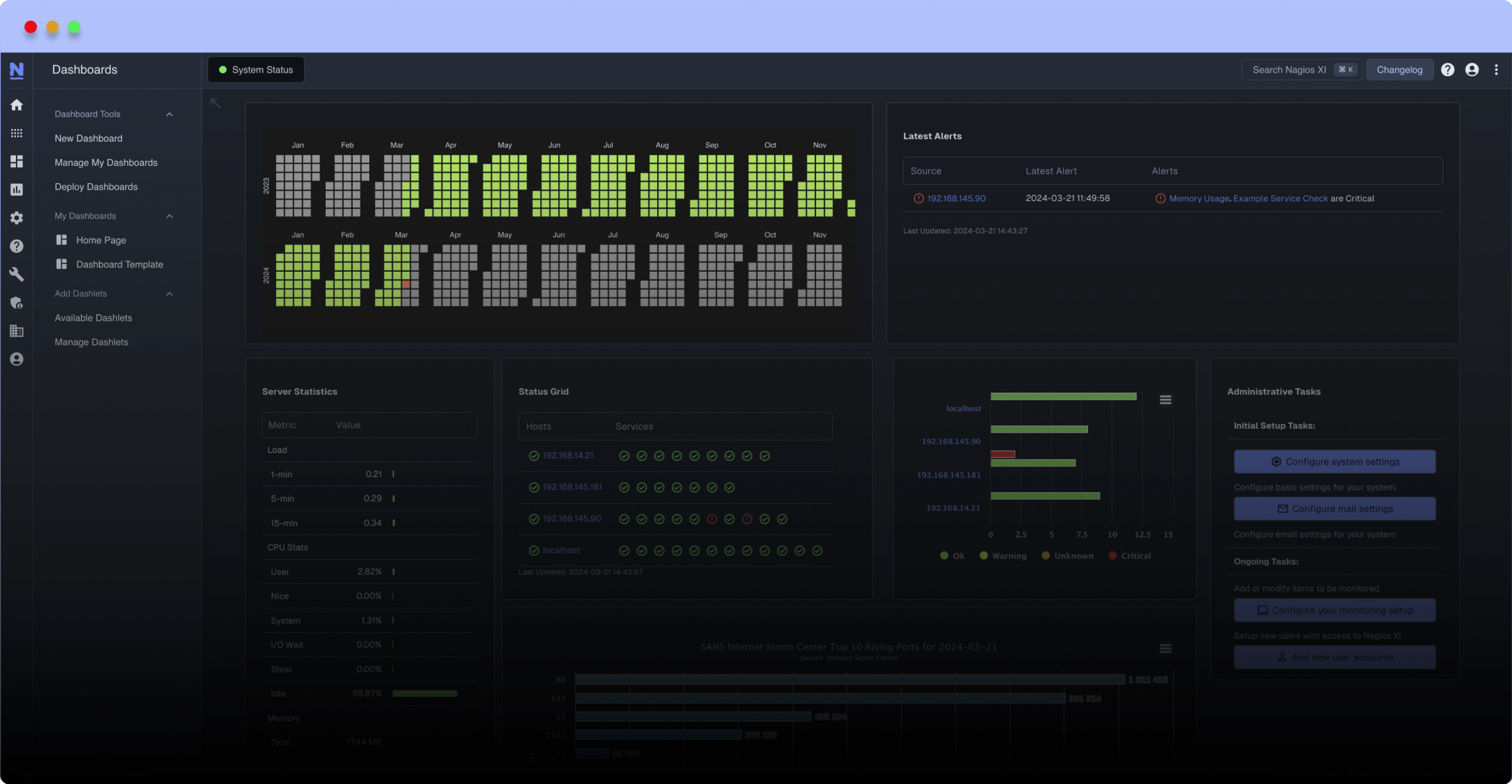
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
Using the YUM Security plugin, it may differentiate between normal and security updates.
Features:
- Using the YUM Security plugin, it may differentiate between normal and security updates.
- Prints the number of available updates (optionally differentiating between normal and security updates).
- By default, returns a CRITICAL state when security updates are found and “ignores” any normal updates. This behaviour may be changed so that normal updates lead to a WARNING state.
- May use the system repository cache, instead of creating/updating a repository cache for the invoking user.
- Repositories may be selectively enabled or disabled for the checks.
- A timeout for the check may be set.
- If the YUM Security plugin is required but not installed, an UNKOWN state will be returned.
- If the output of YUM changes and cannot be parsed anymore, an UNKOWN state will be returned.
Documentation:
Invoking the program with the “--help” or “-h” option prints the documentation.
Invocation:
The original author had this warning in place:
“It was requested to not run as root but some experimentation has shown that package information is generally less reliable when running as a normal user. YUM incorrectly returns less or no security updates, which are shown when run as root. I believe this is due to YUM repository files not being readable by a non-privileged user (especially 3rd party repositories). If you relax the permissions on those repository files it may be possible to run this as a non-root user, but you should first check for differences in results on your systems between running as root or as an ordinary user.”
- Using the YUM Security plugin, it may differentiate between normal and security updates.
- Prints the number of available updates (optionally differentiating between normal and security updates).
- By default, returns a CRITICAL state when security updates are found and “ignores” any normal updates. This behaviour may be changed so that normal updates lead to a WARNING state.
- May use the system repository cache, instead of creating/updating a repository cache for the invoking user.
- Repositories may be selectively enabled or disabled for the checks.
- A timeout for the check may be set.
- If the YUM Security plugin is required but not installed, an UNKOWN state will be returned.
- If the output of YUM changes and cannot be parsed anymore, an UNKOWN state will be returned.
Documentation:
Invoking the program with the “--help” or “-h” option prints the documentation.
Invocation:
The original author had this warning in place:
“It was requested to not run as root but some experimentation has shown that package information is generally less reliable when running as a normal user. YUM incorrectly returns less or no security updates, which are shown when run as root. I believe this is due to YUM repository files not being readable by a non-privileged user (especially 3rd party repositories). If you relax the permissions on those repository files it may be possible to run this as a non-root user, but you should first check for differences in results on your systems between running as root or as an ordinary user.”
Reviews (13)
bytachtler, November 28, 2017
I had to add some fix to this scipt:
in line 304 the is a "limit":
if len(output) > number_total_updates + 25 / OR 25000:
I had to change this value to 50000: because output from
yum --security check-update has about 29000 lines.
in line 304 the is a "limit":
if len(output) > number_total_updates + 25 / OR 25000:
I had to change this value to 50000: because output from
yum --security check-update has about 29000 lines.
byabcklocki, December 15, 2016
I had to add some fix to this scipt:
in line 304 the is a "limit":
if len(output) > number_total_updates + 25:
I had to change this value to 25000: because output from yum --security check_update has about 23000 lines.
in line 304 the is a "limit":
if len(output) > number_total_updates + 25:
I had to change this value to 25000: because output from yum --security check_update has about 23000 lines.
bygiantsquid, May 14, 2013
Worked perfectly until yesterday; I use it with -C --all-updates on Amazon AWS.
As of now it returns "Cannot find summary line in YUM output. Please make sure you have upgraded to the latest version of this plugin. If the problem persists, please contact the author for a fix" and this I am doing now.
What I'd love it to parse is these lines:
sudo yum --security check-update -v
...
There are 40 total update(s) available
Security: kernel-3.2.39-6.88.amzn1.i686 is an installed security update
Security: kernel-3.2.38-5.48.amzn1.i686 is the currently running version
...
Would you be so kind and check if you can include that?
As of now it returns "Cannot find summary line in YUM output. Please make sure you have upgraded to the latest version of this plugin. If the problem persists, please contact the author for a fix" and this I am doing now.
What I'd love it to parse is these lines:
sudo yum --security check-update -v
...
There are 40 total update(s) available
Security: kernel-3.2.39-6.88.amzn1.i686 is an installed security update
Security: kernel-3.2.38-5.48.amzn1.i686 is the currently running version
...
Would you be so kind and check if you can include that?
bystrange, March 29, 2012
I download this plugin in revision 0.7.2 :
http://opensource.is/trac/browser/nagios-plugins/check_yum/
All works
there is a 0.7.3 but i don't test it ...
Thanks
http://opensource.is/trac/browser/nagios-plugins/check_yum/
All works
there is a 0.7.3 but i don't test it ...
Thanks
bycalestyo, March 23, 2012
This version seems to be also patched for RHEL6, but a bit differently than the patch below.
http://opensource.ok.is/trac/browser/nagios-plugins/check_yum/check_yum
http://opensource.ok.is/trac/browser/nagios-plugins/check_yum/check_yum
Augmenting the excellent advice of the previous poster, here is a small diff against check_yum 0.7.1 which will allow the script to continue working with CentOS 5 while also making it compatible with the yum output format of CentOS 6:
*** check_yum.old 2012-03-18 18:58:12.000000000 +0100
--- check_yum 2012-03-18 18:57:36.000000000 +0100
***************
*** 318,326 ****
output = self.run(cmd)
re_security_summary =
! re.compile("Needed d+ of d+ packages, for security")
re_no_security_updates_available =
! re.compile("No packages needed, for security, d+ available")
summary_line_found = False
for line in output:
if re_no_security_updates_available.match(line):
--- 318,326 ----
output = self.run(cmd)
re_security_summary =
! re.compile("Needed d+ of d+ packages,? for security")
re_no_security_updates_available =
! re.compile("No packages needed,? for security[;,] d+ (packages )?available")
summary_line_found = False
for line in output:
if re_no_security_updates_available.match(line):
*** check_yum.old 2012-03-18 18:58:12.000000000 +0100
--- check_yum 2012-03-18 18:57:36.000000000 +0100
***************
*** 318,326 ****
output = self.run(cmd)
re_security_summary =
! re.compile("Needed d+ of d+ packages, for security")
re_no_security_updates_available =
! re.compile("No packages needed, for security, d+ available")
summary_line_found = False
for line in output:
if re_no_security_updates_available.match(line):
--- 318,326 ----
output = self.run(cmd)
re_security_summary =
! re.compile("Needed d+ of d+ packages,? for security")
re_no_security_updates_available =
! re.compile("No packages needed,? for security[;,] d+ (packages )?available")
summary_line_found = False
for line in output:
if re_no_security_updates_available.match(line):
byaugusto, February 5, 2012
I was able to run this properly on Centos 6 with selinux enabled.
I wrote a blog post[1] about how I created the policy and the source of the policy, so anyone can build it.
[1] http://codeforthesoul.blogspot.com/2012/02/selinux-policy-to-run-checkyum.html
I wrote a blog post[1] about how I created the policy and the source of the policy, so anyone can build it.
[1] http://codeforthesoul.blogspot.com/2012/02/selinux-policy-to-run-checkyum.html
@antonio7 this issue is caused by Selinux.
Configure Selinux on your box or disable it in /etc/sysconfig/selinux if it is applicable in your environment.
Configure Selinux on your box or disable it in /etc/sysconfig/selinux if it is applicable in your environment.
Hello,
Thank you for this great plugin but, when I use it with RHEL6 systems, it give me errors
UNKNOWN: Security plugin for yum is required. Try to 'yum install yum-security' and then re-run this plugin. Alternatively, to just alert on any update which does not require the security plugin, try --all-updates even with installing the required package.
and in some other RHEL6 systems it give me
YUM WARNING: Cannot find summary line in yum output. Please make sure you have upgraded to the latest version of this plugin. If the problem persists, please contact the author for a fix
Thanks
Thank you for this great plugin but, when I use it with RHEL6 systems, it give me errors
UNKNOWN: Security plugin for yum is required. Try to 'yum install yum-security' and then re-run this plugin. Alternatively, to just alert on any update which does not require the security plugin, try --all-updates even with installing the required package.
and in some other RHEL6 systems it give me
YUM WARNING: Cannot find summary line in yum output. Please make sure you have upgraded to the latest version of this plugin. If the problem persists, please contact the author for a fix
Thanks
Owner's reply
Should be fixed in recent versions.
bylinux_samurai, October 25, 2011
0 of 1 people found this review helpful
I reviewed this scripts code and tested on several sandbox servers. I then implemented it on multiple CentOS 5.x environments with no problems. This plugin is definitely helpful with quickly pinpointing servers that haven't been patched.
Additionally, I have it only checking every 24 hours, and have alerting turned off except business hours.
Here is our service definition:
-=-=-=-=-=-=-=-=-=-=-=-=-=
define service{
use generic-service
host_name hosta,hostb,hostc
max_check_attempts 3
normal_check_interval 1440
retry_check_interval 120
notification_interval 1440
notification_period workhours
service_description Check_Linux_Updates
check_command check_nrpe!check_yum
}
Additionally, I have it only checking every 24 hours, and have alerting turned off except business hours.
Here is our service definition:
-=-=-=-=-=-=-=-=-=-=-=-=-=
define service{
use generic-service
host_name hosta,hostb,hostc
max_check_attempts 3
normal_check_interval 1440
retry_check_interval 120
notification_interval 1440
notification_period workhours
service_description Check_Linux_Updates
check_command check_nrpe!check_yum
}
After upgrade from CentOS 5.6 to 6.0 check_yum stopped to work.
It looks like NRPE is running in some kind of chrooted environment.
That's why Check_Yum can not find executable /usr/bin/yum and fails.
It looks like NRPE is running in some kind of chrooted environment.
That's why Check_Yum can not find executable /usr/bin/yum and fails.
Owner's reply
This is not a check_yum issue then.
byd_preston215, October 18, 2010
When running the check_yum plugin on Fedora 13 machines, there is a good chance you will come up with this error:
YUM WARNING: Cannot find summary line in yum output. Please make sure you have upgraded to the latest version of this plugin. If the problem persists, please contact the author for a fix
Luckily there is a simple reason for this. The good folks at Fedora just decided to change some words around in the summary output. However, this throws the plugin for a loop since it's looking for specfic text to indicate the summary output (and determine what updates are potentially available). Solution for this is to just change the text so that it matches the summary output of yum on Fedora 13 servers:
On line 323 of the check_yum plugin:
Replace this text:
No packages needed, for security, \d+ available
With this:
No packages needed for security; \d+ packages available
YUM WARNING: Cannot find summary line in yum output. Please make sure you have upgraded to the latest version of this plugin. If the problem persists, please contact the author for a fix
Luckily there is a simple reason for this. The good folks at Fedora just decided to change some words around in the summary output. However, this throws the plugin for a loop since it's looking for specfic text to indicate the summary output (and determine what updates are potentially available). Solution for this is to just change the text so that it matches the summary output of yum on Fedora 13 servers:
On line 323 of the check_yum plugin:
Replace this text:
No packages needed, for security, \d+ available
With this:
No packages needed for security; \d+ packages available


 New Listings
New Listings