Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
NRPE - Nagios Remote Plugin Executor Featured Popular
Current Version
4.0.2
Last Release Date
2020-03-18
Compatible With
- Nagios 1.x
- Nagios 2.x
- Nagios 3.x
- Nagios 4.x
- Nagios XI
Owner
License
GPL
Hits
1430324
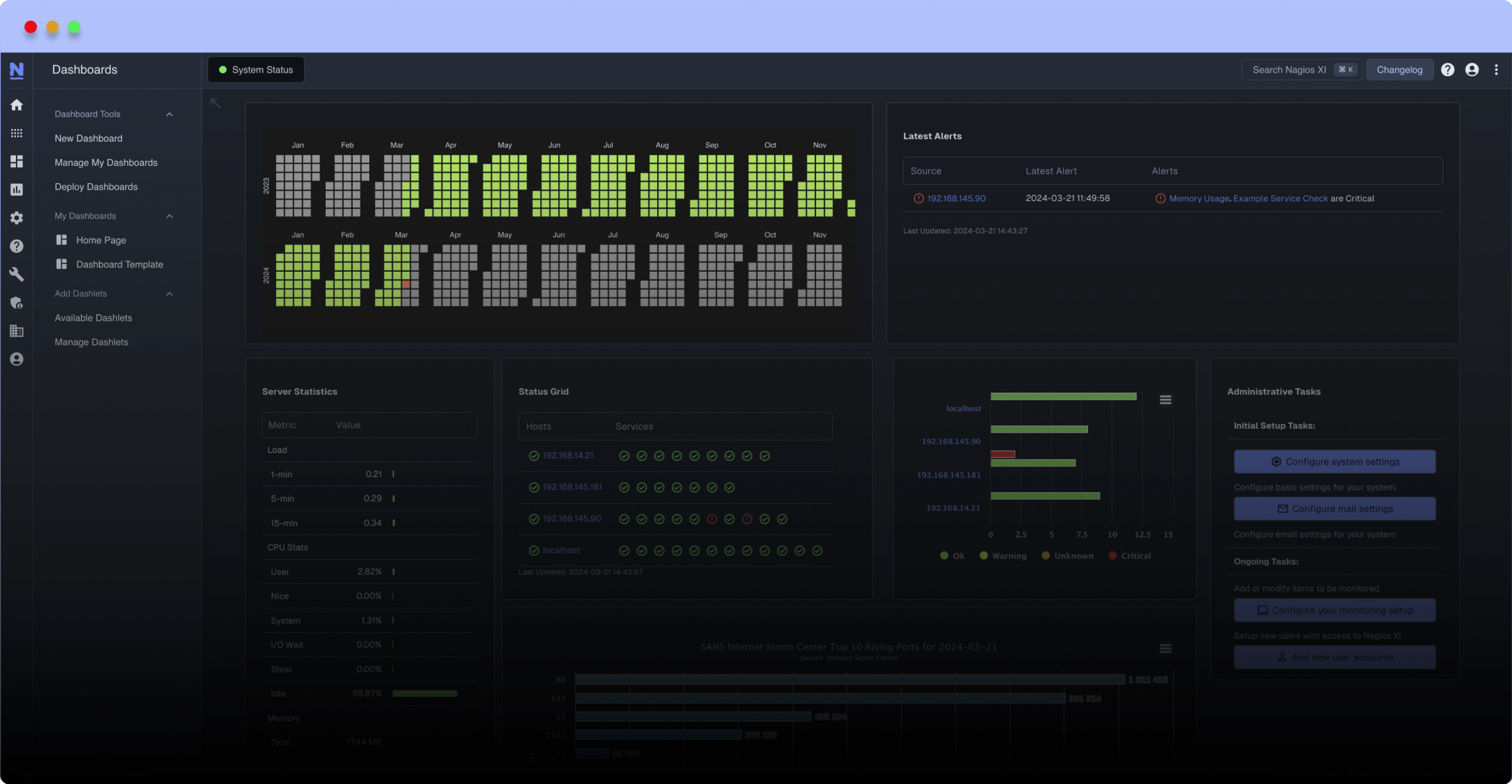
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
Older versions of NRPE can be downloaded from http://sourceforge.net/projects/nagios/files/nrpe-2.x/
Reviews (18)
on our setup the server is running on nrpe V 2.15 and the client is running on V 3.1.0.
on my server
./check_nrpe -H client_ip -n -u -t 30 -c check_load
CHECK_NRPE: Error receiving data from daemon.
with Error: Could not complete SSL handshake with : 1
but i get a valid result when i remove the -n.
is it possible to not to remove the -n and still get a valid result?
on my server
./check_nrpe -H client_ip -n -u -t 30 -c check_load
CHECK_NRPE: Error receiving data from daemon.
with Error: Could not complete SSL handshake with : 1
but i get a valid result when i remove the -n.
is it possible to not to remove the -n and still get a valid result?
byEndlessTundra, October 24, 2016
I tried to compile this on Ubuntu 14.04 and got an error, anybody know how to fix it?
./configure --with-ssl=/usr/bin/openssl --with-ssl-lib=/usr/lib/x86_64-linux-gnu --prefix=/etc/nagios3 --enable-command-args
make all
gcc -g -O2 -I/usr/include/openssl -DHAVE_CONFIG_H -I ../include -I ./../include -o nrpe ./nrpe.c ./utils.c ./acl.c -L/usr/lib/x86_64-linux-gnu -lssl -lcrypto -lnsl
./nrpe.c: In function ‘init_ssl’:
./nrpe.c:319:9: warning: format ‘%s’ expects argument of type ‘char *’, but argument 4 has type ‘int’ [-Wformat=]
sslprm.cert_file, ERR_error_string(x, NULL));
^
./nrpe.c: In function ‘handle_conn_ssl’:
./nrpe.c:1754:9: warning: format ‘%s’ expects argument of type ‘char *’, but argument 4 has type ‘int’ [-Wformat=]
remote_host, ERR_reason_error_string(x));
^
./nrpe.c: In function ‘main’:
./nrpe.c:168:9: warning: ignoring return value of ‘getcwd’, declared with attribute warn_unused_result [-Wunused-result]
getcwd(config_file, sizeof(config_file));
^
./nrpe.c: In function ‘set_stdio_sigs’:
./nrpe.c:553:7: warning: ignoring return value of ‘chdir’, declared with attribute warn_unused_result [-Wunused-result]
chdir("/");
^
./nrpe.c: In function ‘my_system’:
./nrpe.c:1994:6: warning: ignoring return value of ‘pipe’, declared with attribute warn_unused_result [-Wunused-result]
pipe(fd); /* create a pipe */
^
In file included from ./nrpe.c:27:0:
../include/config.h:110:28: warning: ignoring return value of ‘seteuid’, declared with attribute warn_unused_result [-Wunused-result]
#define SETEUID(id) seteuid(id)
^
./nrpe.c:2026:3: note: in expansion of macro ‘SETEUID’
SETEUID(0); /* get root back so the next call works correctly */
^
./nrpe.c:2050:9: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(fd[1], buffer, strlen(buffer) + 1);
^
./nrpe.c:2058:10: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(fd[1], buffer, bytes_read);
^
./nrpe.c:2061:9: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(fd[1], "�", 1);
^
./nrpe.c: In function ‘write_pid_file’:
./nrpe.c:2267:8: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(fd, pbuf, strlen(pbuf));
^
In file included from ./nrpe.c:27:0:
./nrpe.c: In function ‘remove_pid_file’:
../include/config.h:110:28: warning: ignoring return value of ‘seteuid’, declared with attribute warn_unused_result [-Wunused-result]
#define SETEUID(id) seteuid(id)
^
./nrpe.c:2286:2: note: in expansion of macro ‘SETEUID’
SETEUID(0); /* get root back so we can delete the pid file */
^
gcc -g -O2 -I/usr/include/openssl -DHAVE_CONFIG_H -I ../include -I ./../include -o check_nrpe ./check_nrpe.c ./utils.c -L/usr/lib/x86_64-linux-gnu -lssl -lcrypto -lnsl
./check_nrpe.c: In function ‘connect_to_remote’:
./check_nrpe.c:926:9: warning: format ‘%s’ expects argument of type ‘char *’, but argument 4 has type ‘int’ [-Wformat=]
rem_host, ERR_reason_error_string(x));
^
./check_nrpe.c: In function ‘alarm_handler’:
./check_nrpe.c:1457:7: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(STDOUT_FILENO, msg1, sizeof(msg1) - 1);
^
./check_nrpe.c:1458:7: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(STDOUT_FILENO, text, lth1);
^
./check_nrpe.c:1459:7: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(STDOUT_FILENO, msg2, sizeof(msg2) - 1);
^
./check_nrpe.c:1460:7: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(STDOUT_FILENO, timeout_txt, lth2);
^
./check_nrpe.c:1461:7: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(STDOUT_FILENO, msg3, sizeof(msg3) - 1);
./configure --with-ssl=/usr/bin/openssl --with-ssl-lib=/usr/lib/x86_64-linux-gnu --prefix=/etc/nagios3 --enable-command-args
make all
gcc -g -O2 -I/usr/include/openssl -DHAVE_CONFIG_H -I ../include -I ./../include -o nrpe ./nrpe.c ./utils.c ./acl.c -L/usr/lib/x86_64-linux-gnu -lssl -lcrypto -lnsl
./nrpe.c: In function ‘init_ssl’:
./nrpe.c:319:9: warning: format ‘%s’ expects argument of type ‘char *’, but argument 4 has type ‘int’ [-Wformat=]
sslprm.cert_file, ERR_error_string(x, NULL));
^
./nrpe.c: In function ‘handle_conn_ssl’:
./nrpe.c:1754:9: warning: format ‘%s’ expects argument of type ‘char *’, but argument 4 has type ‘int’ [-Wformat=]
remote_host, ERR_reason_error_string(x));
^
./nrpe.c: In function ‘main’:
./nrpe.c:168:9: warning: ignoring return value of ‘getcwd’, declared with attribute warn_unused_result [-Wunused-result]
getcwd(config_file, sizeof(config_file));
^
./nrpe.c: In function ‘set_stdio_sigs’:
./nrpe.c:553:7: warning: ignoring return value of ‘chdir’, declared with attribute warn_unused_result [-Wunused-result]
chdir("/");
^
./nrpe.c: In function ‘my_system’:
./nrpe.c:1994:6: warning: ignoring return value of ‘pipe’, declared with attribute warn_unused_result [-Wunused-result]
pipe(fd); /* create a pipe */
^
In file included from ./nrpe.c:27:0:
../include/config.h:110:28: warning: ignoring return value of ‘seteuid’, declared with attribute warn_unused_result [-Wunused-result]
#define SETEUID(id) seteuid(id)
^
./nrpe.c:2026:3: note: in expansion of macro ‘SETEUID’
SETEUID(0); /* get root back so the next call works correctly */
^
./nrpe.c:2050:9: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(fd[1], buffer, strlen(buffer) + 1);
^
./nrpe.c:2058:10: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(fd[1], buffer, bytes_read);
^
./nrpe.c:2061:9: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(fd[1], "�", 1);
^
./nrpe.c: In function ‘write_pid_file’:
./nrpe.c:2267:8: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(fd, pbuf, strlen(pbuf));
^
In file included from ./nrpe.c:27:0:
./nrpe.c: In function ‘remove_pid_file’:
../include/config.h:110:28: warning: ignoring return value of ‘seteuid’, declared with attribute warn_unused_result [-Wunused-result]
#define SETEUID(id) seteuid(id)
^
./nrpe.c:2286:2: note: in expansion of macro ‘SETEUID’
SETEUID(0); /* get root back so we can delete the pid file */
^
gcc -g -O2 -I/usr/include/openssl -DHAVE_CONFIG_H -I ../include -I ./../include -o check_nrpe ./check_nrpe.c ./utils.c -L/usr/lib/x86_64-linux-gnu -lssl -lcrypto -lnsl
./check_nrpe.c: In function ‘connect_to_remote’:
./check_nrpe.c:926:9: warning: format ‘%s’ expects argument of type ‘char *’, but argument 4 has type ‘int’ [-Wformat=]
rem_host, ERR_reason_error_string(x));
^
./check_nrpe.c: In function ‘alarm_handler’:
./check_nrpe.c:1457:7: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(STDOUT_FILENO, msg1, sizeof(msg1) - 1);
^
./check_nrpe.c:1458:7: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(STDOUT_FILENO, text, lth1);
^
./check_nrpe.c:1459:7: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(STDOUT_FILENO, msg2, sizeof(msg2) - 1);
^
./check_nrpe.c:1460:7: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(STDOUT_FILENO, timeout_txt, lth2);
^
./check_nrpe.c:1461:7: warning: ignoring return value of ‘write’, declared with attribute warn_unused_result [-Wunused-result]
write(STDOUT_FILENO, msg3, sizeof(msg3) - 1);
byajaywil, June 6, 2016
Is there a firm release date scheduled for 3.0? You mentioned back at the end of April a few weeks but I am not aware of it being released as of June.
We are eagerly anticipating the security vulnerability fix outlined here:
https://www.tenable.com/plugins/index.php?view=single&id=73757
We are eagerly anticipating the security vulnerability fix outlined here:
https://www.tenable.com/plugins/index.php?view=single&id=73757
byjfrickson, April 28, 2016
1 of 1 people found this review helpful
Responding to review by @stefanlasiewski :
I started working for Nagios fairly recently and am in charge of development for core, plugins, ndo, nsca, and nrpe. I've been putting quite a lot of work into most of those and nrpe, in particular, has gotten a lot of attention.
The new version 3.0 (which should be released in a few weeks) addresses the payload size. It will handle 64K.
I wasn't aware of that particular security vulnerability, but I am now. Thank you. It will be addressed for the 3.0 release.
Other things that will be in 3.0:
o Better signal handling
o A bunch of bug fixes
o Major update to SSL/TLS processing
o Some code changes and major configure changes to handle multiple platforms, including different Linux distributions, AIX, HP-UX, Solaris, Mac OS X, and the *BSD's.
So yes, NRPE was not getting the attention it deserved but it is now!
I started working for Nagios fairly recently and am in charge of development for core, plugins, ndo, nsca, and nrpe. I've been putting quite a lot of work into most of those and nrpe, in particular, has gotten a lot of attention.
The new version 3.0 (which should be released in a few weeks) addresses the payload size. It will handle 64K.
I wasn't aware of that particular security vulnerability, but I am now. Thank you. It will be addressed for the 3.0 release.
Other things that will be in 3.0:
o Better signal handling
o A bunch of bug fixes
o Major update to SSL/TLS processing
o Some code changes and major configure changes to handle multiple platforms, including different Linux distributions, AIX, HP-UX, Solaris, Mac OS X, and the *BSD's.
So yes, NRPE was not getting the attention it deserved but it is now!
bystefanlasiewski, April 27, 2016
This tool works, but it hasn't received an update since 2013.
Functionally, NRPE can only handle a payload of 1024 bytes, which limits the amount of data that you can receive on your Nagios server. There have been a couple security reports with NRPE since the last release (See https://www.opsview.com/resources/blog/nagios-nrpe-security-vulnerability ), and it's not clear if Nagios.com ever patched their code in response to these reports.
Functionally, NRPE can only handle a payload of 1024 bytes, which limits the amount of data that you can receive on your Nagios server. There have been a couple security reports with NRPE since the last release (See https://www.opsview.com/resources/blog/nagios-nrpe-security-vulnerability ), and it's not clear if Nagios.com ever patched their code in response to these reports.
byjotagera, March 8, 2016
Nrpe is excelent.
I think i got a error on version 2.15.
It did´nt obey the user on nrpe.fg to fork and execute local checks.
It uses always nagios.
I think i got a error on version 2.15.
It did´nt obey the user on nrpe.fg to fork and execute local checks.
It uses always nagios.
byzecarlos, July 11, 2015
This is a very useful tool to monitor remote servers and performs better than using SSH.
However I believe this issue still applies http://legalhackers.com/advisories/nagios-nrpe.txt
Not a big deal if you restrict access to the nagios server and keep arguments disabled, but still... I hope to see a new version out soon with a fix.
However I believe this issue still applies http://legalhackers.com/advisories/nagios-nrpe.txt
Not a big deal if you restrict access to the nagios server and keep arguments disabled, but still... I hope to see a new version out soon with a fix.
byproliant, November 16, 2014
Version: 2.14, 2.15
Source: nrpe-2.1[4|5].tar.gz
Platform: Centos 6.5 x64 (Nagios client)
Compile1: ./configure --enable-ssl --with-nrpe-user=nagios --with-nrpe-group=nagios --with-nagios-user=nagios --with-nagios-group=nagios --libexecdir=/opt/nagios/libexec/ --bindir=/opt/nagios/bin/ --prefix=/opt/nagios
Compile2: ./configure --enable-ssl --with-nrpe-user=nagios --with-nrpe-group=nagios --with-nagios-user=nagios --with-nagios-group=nagios --libexecdir=/opt/nagios/libexec/ --bindir=/opt/nagios/bin/ --prefix=/opt/nagios --with-cacert-file --with-privatekey-file
Conf file: /opt/nagios/etc/nrpe.cfg
log_facility=daemon
pid_file=/var/run/nrpe.pid
server_port=5666
nrpe_user=nagios
nrpe_group=nagios
allowed_hosts=127.0.0.1,10.0.194.9
cert_file=/opt/nagios/etc/server.crt # ient, /var/log/message reports unknown option when restart nrpe daemon:
Nov 17 11:30:30 localhost nrpe[1111]: Unknown option specified in config file '/opt/icinga/etc/nrpe.cfg' - Line 92
Nov 17 11:30:30 localhost nrpe[1111]: Unknown option specified in config file '/opt/icinga/etc/nrpe.cfg' - Line 93
Nov 17 11:30:30 localhost nrpe[1111]: Unknown option specified in config file '/opt/icinga/etc/nrpe.cfg' - Line 94
Nov 17 11:30:30 localhost nrpe[1112]: Starting up daemon
Nov 17 11:30:30 localhost nrpe[1112]: Server listening on 0.0.0.0 port 5666.
Nov 17 11:30:30 localhost nrpe[1112]: Server listening on :: port 5666.
Nov 17 11:30:30 localhost nrpe[1112]: Listening for connections on port 0
Nov 17 11:30:30 localhost nrpe[1112]: Allowing connections from: 127.0.0.1,10.0.194.9
Question:
Do these parameters exist in the tarball? (i.e. --with-cacert-file --with-privatekey-file)
Hope to hear from you soon.
Source: nrpe-2.1[4|5].tar.gz
Platform: Centos 6.5 x64 (Nagios client)
Compile1: ./configure --enable-ssl --with-nrpe-user=nagios --with-nrpe-group=nagios --with-nagios-user=nagios --with-nagios-group=nagios --libexecdir=/opt/nagios/libexec/ --bindir=/opt/nagios/bin/ --prefix=/opt/nagios
Compile2: ./configure --enable-ssl --with-nrpe-user=nagios --with-nrpe-group=nagios --with-nagios-user=nagios --with-nagios-group=nagios --libexecdir=/opt/nagios/libexec/ --bindir=/opt/nagios/bin/ --prefix=/opt/nagios --with-cacert-file --with-privatekey-file
Conf file: /opt/nagios/etc/nrpe.cfg
log_facility=daemon
pid_file=/var/run/nrpe.pid
server_port=5666
nrpe_user=nagios
nrpe_group=nagios
allowed_hosts=127.0.0.1,10.0.194.9
cert_file=/opt/nagios/etc/server.crt # ient, /var/log/message reports unknown option when restart nrpe daemon:
Nov 17 11:30:30 localhost nrpe[1111]: Unknown option specified in config file '/opt/icinga/etc/nrpe.cfg' - Line 92
Nov 17 11:30:30 localhost nrpe[1111]: Unknown option specified in config file '/opt/icinga/etc/nrpe.cfg' - Line 93
Nov 17 11:30:30 localhost nrpe[1111]: Unknown option specified in config file '/opt/icinga/etc/nrpe.cfg' - Line 94
Nov 17 11:30:30 localhost nrpe[1112]: Starting up daemon
Nov 17 11:30:30 localhost nrpe[1112]: Server listening on 0.0.0.0 port 5666.
Nov 17 11:30:30 localhost nrpe[1112]: Server listening on :: port 5666.
Nov 17 11:30:30 localhost nrpe[1112]: Listening for connections on port 0
Nov 17 11:30:30 localhost nrpe[1112]: Allowing connections from: 127.0.0.1,10.0.194.9
Question:
Do these parameters exist in the tarball? (i.e. --with-cacert-file --with-privatekey-file)
Hope to hear from you soon.
byfriendyogi, August 12, 2014
Why does this page says compatible with upto Nagios 3.0?
NRPE used to work with Nagios 3.0 in our environment. But ever since we upgraded to Nagios core 4.0.7 NRPE started giving error:
Aug 13 08:55:25 web1 xinetd[6076]: START: nrpe pid=4422 from=::ffff:210.21.7.1
Aug 13 08:55:25 web1 xinetd[4422]: FAIL: nrpe address from=::ffff:210.21.7.1
Aug 13 08:55:25 web1 xinetd[6076]: EXIT: nrpe status=0 pid=4422 duration=0(sec)
Note: IP is allowed in xinetd config.
NRPE used to work with Nagios 3.0 in our environment. But ever since we upgraded to Nagios core 4.0.7 NRPE started giving error:
Aug 13 08:55:25 web1 xinetd[6076]: START: nrpe pid=4422 from=::ffff:210.21.7.1
Aug 13 08:55:25 web1 xinetd[4422]: FAIL: nrpe address from=::ffff:210.21.7.1
Aug 13 08:55:25 web1 xinetd[6076]: EXIT: nrpe status=0 pid=4422 duration=0(sec)
Note: IP is allowed in xinetd config.
bymtarkowski, May 22, 2014
why is it I'm getting this using NRPE 2.15?
# /usr/local/nagios/libexec/check_nrpe -H localhost
CHECK_NRPE: Error - Could not complete SSL handshake.
but, when I try
#/usr/local/nagios/libexec/check_nrpe -H 127.0.0.1
NRPE v2.15
Solution - you need to add your server IP to the allowed_hosts parameter under nrpe.cfg file on the host being monitored.
allowed_hosts=127.0.0.1,
# /usr/local/nagios/libexec/check_nrpe -H localhost
CHECK_NRPE: Error - Could not complete SSL handshake.
but, when I try
#/usr/local/nagios/libexec/check_nrpe -H 127.0.0.1
NRPE v2.15
Solution - you need to add your server IP to the allowed_hosts parameter under nrpe.cfg file on the host being monitored.
allowed_hosts=127.0.0.1,
byvjbangis, September 26, 2013
why is it I'm getting this using NRPE 2.15?
# /usr/local/nagios/libexec/check_nrpe -H localhost
CHECK_NRPE: Error - Could not complete SSL handshake.
but, when I try
#/usr/local/nagios/libexec/check_nrpe -H 127.0.0.1
NRPE v2.15
# /usr/local/nagios/libexec/check_nrpe -H localhost
CHECK_NRPE: Error - Could not complete SSL handshake.
but, when I try
#/usr/local/nagios/libexec/check_nrpe -H 127.0.0.1
NRPE v2.15
Works likle a dream on Linux.
Initially, the compile failed on AIX due to missing SSL libraries. To get around this, I modified the line below in the 'configure' script and that seemed to fix it...
soext="a"
Initially, the compile failed on AIX due to missing SSL libraries. To get around this, I modified the line below in the 'configure' script and that seemed to fix it...
soext="a"
Flexibility of NRPE is beyond any other plugin .. Very much useful...
bynkadel, March 24, 2013
2 of 8 people found this review helpful
This is one of the basic packages I use in every large environment, for Nagios or Icinga monitoring and easy admin checking. Three are 3 small bugs:
* NRPE should have its own user, not share the "nagios" user. That causes confusion with ownership of configuration files and the "nagios" user itself.
* NRPE should have its config files in /etc/nrpe, not /etc/nagios. Again, this causes confusion with who manages the files in /etc/nagios and makes source control and package management much more awkward.
* The default location of "/usr/lib/nagios/plugins" should be set based on architecture. It's /usr/lib64/nagios/plugins on most x86_64 systems.
* NRPE should have its own user, not share the "nagios" user. That causes confusion with ownership of configuration files and the "nagios" user itself.
* NRPE should have its config files in /etc/nrpe, not /etc/nagios. Again, this causes confusion with who manages the files in /etc/nagios and makes source control and package management much more awkward.
* The default location of "/usr/lib/nagios/plugins" should be set based on architecture. It's /usr/lib64/nagios/plugins on most x86_64 systems.
Not sure why this page hasn't been updated with the latest version - you can find it here:
http://www.nagios.org/news/77-news-announcements/345-nrpe-214-released
http://www.nagios.org/news/77-news-announcements/345-nrpe-214-released
NRPE is hands down, the best remote plugin executor for Nagios.
I use NRPE on few hosts, it works good! Just use it - and you'll be happy.
VisMon
VisMon


 New Listings
New Listings