Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
check_rootkit
Owner
Website
Hits
151427
Files:
| File | Description |
|---|---|
| check_rootkit.gz | Place this script in your libexec directory. Documentation in the script. |
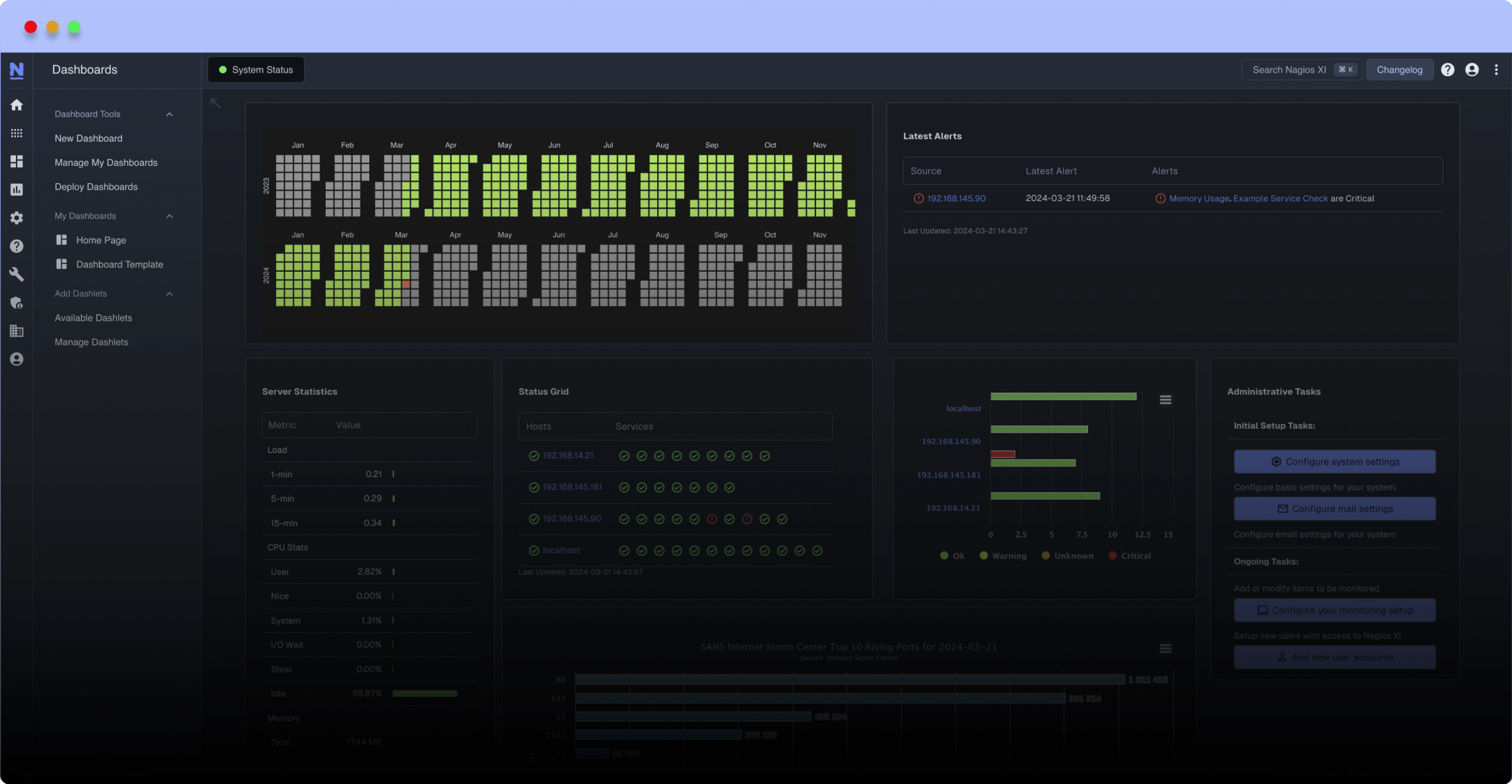
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
A constant thread - a security breach.
This small plugin uses the capabilities of the "Rootkit Hunter", an open source solution downloadable from http://sourceforge.net/projects/rkhunter/
The plugin just starts the program rkhunter (you have to put the program in your /etc/sudoers) and returns a warning or an alert - or an ok if anything is fine.
The command line in the perl script has to be modified conforming your needs. Please read the documentation from rootkit hunter carefully.
This small plugin uses the capabilities of the "Rootkit Hunter", an open source solution downloadable from http://sourceforge.net/projects/rkhunter/
The plugin just starts the program rkhunter (you have to put the program in your /etc/sudoers) and returns a warning or an alert - or an ok if anything is fine.
The command line in the perl script has to be modified conforming your needs. Please read the documentation from rootkit hunter carefully.
Reviews (2)
1) double gzipped
2) I had to remove the --allow-ssh-root option
3) add an --nomow option, so that running it does not generate an email.
2) I had to remove the --allow-ssh-root option
3) add an --nomow option, so that running it does not generate an email.
1. This file seems to be gzipped twice. To unzip, use:
gzip -cd check_rootkit.gz | gzip -d - > check_rootkit
2. Also, my rkhunter binary was in /usr/bin/rkhunter, not in /usr/local/bin/rkhunter.
3. I had to change parts of line 61 in the script to sudo "rkhunter --quiet --check", as my rkhunter version did not know the allow-ssh-root-user option (and I didn't want it anyways).
Besides that, nice script!
gzip -cd check_rootkit.gz | gzip -d - > check_rootkit
2. Also, my rkhunter binary was in /usr/bin/rkhunter, not in /usr/local/bin/rkhunter.
3. I had to change parts of line 61 in the script to sudo "rkhunter --quiet --check", as my rkhunter version did not know the allow-ssh-root-user option (and I didn't want it anyways).
Besides that, nice script!


 New Listings
New Listings