Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
check_fortigate.pl: fortigate,fortimail, fortianalyzer
- Nagios 1.x
- Nagios 2.x
- Nagios 3.x
- Nagios 4.x
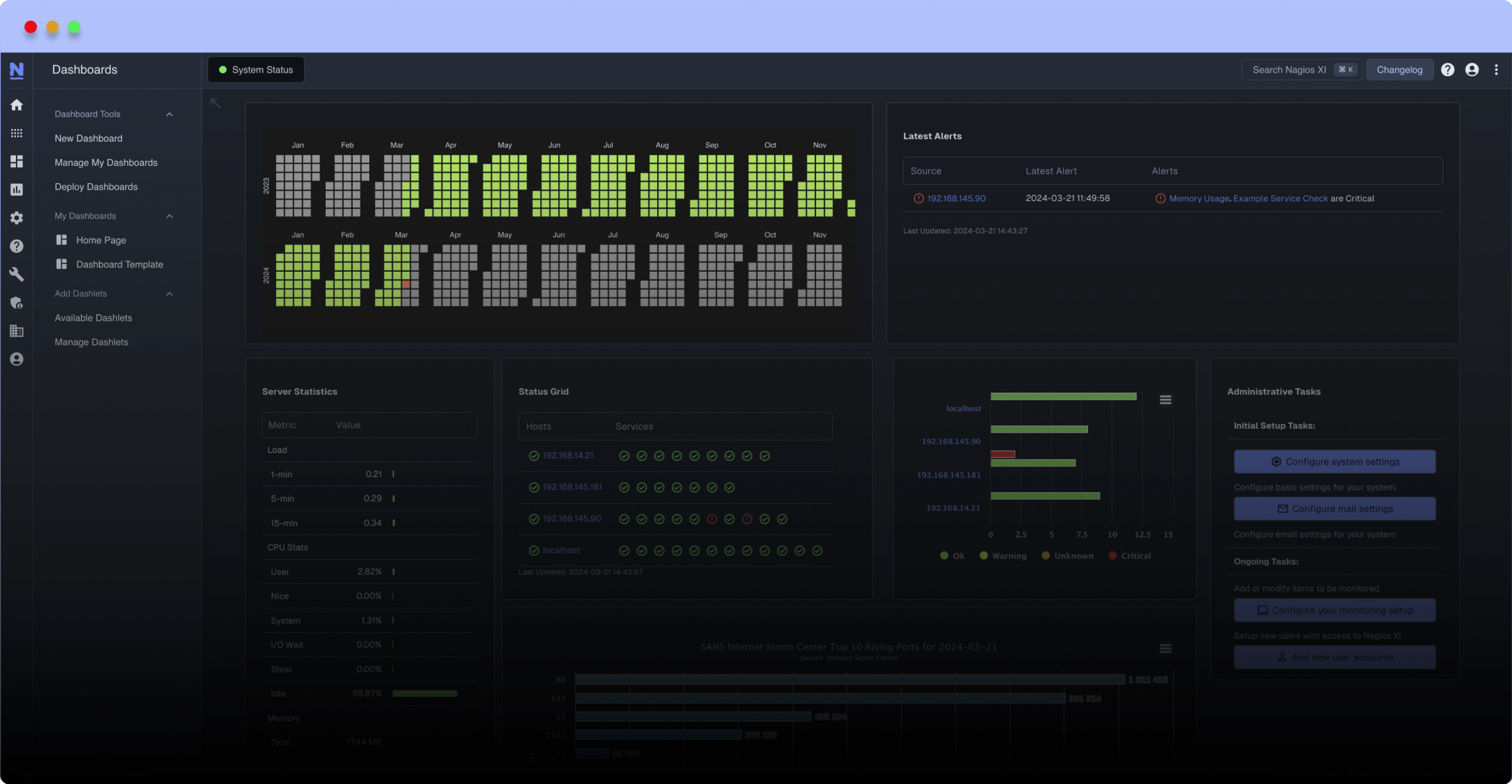
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
Usage:
check_fortigate.pl -H -C -T [-w|-c|-S|-s|-R|-M|-V|-?]
Options:
-H --host STRING or IPADDRESS Check interface on the indicated host
-P --port INTEGER Port of indicated host, defaults to 161
-v --version STRING SNMP Version, defaults to SNMP v2, v1-v3 supported
-T --type STRING CPU, MEM, Ses, VPN, Cluster, Firmware, HW, ..
-S --serial STRING Primary serial number
-s --slave get values of slave
-w --warning INTEGER Warning threshold, applies to cpu, mem, session, firmware
-c --critical INTEGER Critical threshold, applies to cpu, mem, session, firmware
-R --reset Resets ip file (cluster only)
-M --mode STRING Output-Mode: 0 => just print, 1 => print and show failed tunnel, 2 => critical
-V --vpnmode STRING VPN-Mode: both => IPSec & SSL/OpenVPN, ipsec => IPSec only, ssl => SSL/OpenVPN only
SNMP v1/v2c only
-C --community STRING Community-String for SNMP, only at SNMP v1/v2c, defaults to public
SNMP v3 only
-U --username STRING Username
-A --authpassword STRING auth password
-a --authprotocol STRING auth algorithm, defaults to sha
-X --privpassword STRING private password
-x --privprotocol STRING private algorithm, defaults to aes
-? --help Returns full help text
Requires Net::SNMP, List::Compare, Getopt::Long, Pod::Usage, Switch
This plugin checks FortiGate devices via SNMP (enable snmp, configure community and allow snmp access on client lan)
* Update 2016-05-13: added FortiAnalyzer support, improved Cluster-State check and added Firmware-Check
* Update 2015-03-11: added WTP support (thanks to Mikael)
* Update 2015-02-26: added SNMP v3 support
* Update 2013-01-16: changed CPU OID, added net usage
- List::Compare (Ubuntu/Debian: liblist-compare-perl)
- Net::SNMP (Ubuntu/Debian: libnet-snmp-perl)
NAME
Check Fortinet FortiGate Appliances
SYNOPSIS
check_fortigate.pl -H -C -T [-w|-c|-S|-s|-R|-M|-V|-?]
Options:
-H --host STRING or IPADDRESS Check interface on the indicated host
-P --port INTEGER Port of indicated host, defaults to 161
-v --version STRING SNMP Version, defaults to SNMP v2, v1-v3 supported
-T --type STRING CPU, MEM, Ses, VPN, Cluster, firmware, hw, disk
-S --serial STRING Primary serial number
-s --slave get values of slave
-w --warning INTEGER Warning threshold, applies to cpu, mem, session.
-c --critical INTEGER Critical threshold, applies to cpu, mem, session.
-R --reset Resets ip file (cluster only)
-M --mode STRING Output-Mode: 0 => just print, 1 => print and show failed tunnel, 2 => critical
-V --vpnmode STRING VPN-Mode: both => IPSec & SSL/OpenVPN, ipsec => IPSec only, ssl => SSL/OpenVPN only
SNMP v1/v2c only
-C --community STRING Community-String for SNMP, only at SNMP v1/v2c, defaults to public
SNMP v3 only
-U --username STRING
-A --authpassword STRING auth password
-a --authprotocol STRING auth algorithm, defaults to sha
-X --privpassword STRING private password
-x --privprotocol STRING private algorithm, defaults to aes
-? --help Returns full help text
OPTIONS
-H--host
STRING or IPADDRESS - Check interface on the indicated host.
-C|--community
STRING - Community-String for SNMP
-T|--type
STRING - CPU, MEM, Ses, VPN, Cluster, Firmware, fazmem, fazcpu
-S|--serial
STRING - Primary serial number.
-s|--slave
BOOL - Get values of slave
-w|--warning
INTEGER - Warning threshold, applies to cpu, net, mem, session.
-c|--critical
INTEGER - Critical threshold, applies to cpu, net, mem, session.
-R|--reset
BOOL - Resets ip file (cluster only)
-M|--mode
STRING - Output-Mode: 0 => just print, 1 => print and show
failed tunnel, 2 => critical
-V|--vpnmode
STRING - VPN-Mode: both => IPSec & SSL/OpenVPN, ipsec => IPSec
only, ssl => SSL/OpenVPN only
DESCRIPTION
This plugin checks Fortinet FortiGate devices via SNMP
From Web:
1. Select Network -> Interface -> Local interface
2. Administrative Access: Enable SNMP
3. Select Config -> SNMP
4. Enable SNMP, fill your details
5. SNMP v1/v2c: Create new
6. Configure for your needs, Traps are not required for this plugin!
From CLI:
config system interface
edit "internal"
set allowaccess ping https ssh snmp fgfm
next
end
config system snmp sysinfo
set description "DMZ1 FortiGate 300C"
set location "Room 404"
set conctact-info "BOFH"
set status enable
end
config system snmp community
edit 1
set events cpu-high mem-low fm-if-change
config hosts
edit 1
set interface "internal"
set ip %SNMP Client IP%
next
end
set name "public"
set trap-v1-status disable
set trap-v2c-status disable
next
end
Thats it!
Samples:
To use SNMPv3 just replace "-C public" with "-v 3 -U username -A this_is_auth_string -a sha -x aes128 -X this_is_priv_string"
Cluster:
$ check_fortigate.pl -H 192.168.123.100 -C public -T cluster
OK: Fortinet 300C (Master: FGSERIALMASTER, Slave: FGSERIALSLAVE): HA (Active/Passive) is active
- Warning if unknown node appears
- Critical if single node
- Optional: Critical, if preferred master (-S Serial) is not master
CPU:
$ check_fortigate.pl -H 192.168.123.100 -C public -T cpu
OK: Fortinet 300C (Master: FGSERIALMASTER) CPU is okay: 1%|'cpu'=1%;80;90
CPU-Slave:
$ check_fortigate.pl -H 192.168.123.100 -C public -T cpu -s
OK: Fortinet 300C (Master: FGSERIALMASTER) slave_CPU is okay: 5%|'slave_cpu'=5%;80;90
- Defaults: 80%/90%
Memory:
$ check_fortigate.pl -H 192.168.123.100 -C public -T mem
OK: Fortinet 300C (Master: FGSERIALMASTER) Memory is okay: 29%|'memory'=29%;80;90
Memory-Slave:
$ check_fortigate.pl -H 192.168.123.100 -C public -T mem
OK: Fortinet 300C (Master: FGSERIALMASTER) slave_Memory is okay: 29%|'slave_memory'=29%;80;90
- Defaults: 80%/90%
Sessions:
$ check_fortigate.pl -H 192.168.123.100 -C public -T ses
WARNING: Fortinet 300C (Master: FGSERIALMASTER) Session is warning: 85|'session'=85;80;90
Sessions-Slave:
$ check_fortigate.pl -H 192.168.123.100 -C public -T ses -s
WARNING: Fortinet 300C (Master: FGSERIALMASTER) slave_Session is warning: 85|'slave_session'=85;80;90
- Defaults: 80/90
VPN:
Both: $ check_fortigate.pl -H 192.168.123.200 -C public -T vpn -V both -M 1
OK: Fortigate 100D (Master: FGSERIALMASTER): Active SSL-VPN Connections/Tunnels: 0/0: IPSEC Tunnels: Configured/Active: 4/3 , Static_Sample_p2 down|'ActiveSSL-VPN'=0 'ActiveIPSEC'=3
SSL: $ check_fortigate.pl -H 192.168.123.100 -C public -T vpn -V ssl -M 0
OK: Fortinet 300C (Master: FGSERIALMASTER): Active SSL-VPN Connections/Tunnels: 0/0|'ActiveSSL-VPN'=0 'ActiveIPSEC'=0
IPSec: $ check_fortigate.pl -H 192.168.123.200 -C public -T vpn -V ipsec -M 2
WARNING: Fortigate 100D (Master: FGSERIALMASTER): IPSEC Tunnels: Configured/Active: 4/3 , Static_Sample_p2 down|'ActiveSSL-VPN'=0 'ActiveIPSEC'=3
- Warning if Mode (-M) > 1 and ipsec tunnel is down
Can I use it with snmp v3 with authentication?
thx!
Today i released v1.4 with SNMPv3 Support :-)
the 255 out of bounds messages is because you are not creating an _SNMP_COMMUNITY variable in the host definition. e.g.:
define host{
use generic-switch ; Inherit default values from a template
host_name FG80CXXXXXXX ; The name we're giving to this host
alias Fortigate Firewall ; A longer name associated with the host
_SNMP_COMMUNITY public
address 192.168.1.1 ; IP address of the host
}
And then to check IPSEC VPN:
define service{
use generic-service
host_name FG80CXXXXXXXXX
service_description IPSec VPN Status
check_command check_fortigate_vpn!ipsec
contact_groups twilio_sms_alert
}
However, there is a problem: as stated before, it workes perfectly well when executed manually, but fails when it is run by Nagios. I disabled EPN and the error message changed. Now it reads as:
"Return code of 255 is out of bounds"
And here is what I have in my logs:
"Warning: Return code of 255 for check of service 'CPU load' on host 'FG-XXX'was out of bounds."
It would be really-really nice to make this work!
Hey UncleIS,
this plugin creates a Serial File on first run to compare against for failed clusters..
I assume you called the plugin manually as root if so, please delete folder FortiSerial in your plugins folder
!Never try monitoring plugins as root :)!
If you enable Debugging in Nagios, you get the following error:
---
HOST: somehost, SERVICE: CPU, CHECK TYPE: Active, OPTIONS: 0, SCHEDULED: Yes, RESCHEDULE: Yes, EXITED OK: No, RETURN CODE: 3, OUTPUT: **ePN failed to compile /some/dir/plugins/check_fortigate.pl: "String found where operator expected at (eval 17) line 94, near "case "cpu""" at /usr/lib/nagios3/p1.pl line 250.
---
The workaround is to disable the ePN by inserting the following String an the second line in the check_fortigate.pl-script
---
# nagios: -epn
---
Thanks for noticing, i added # nagios -epn to defaults
I should switch switch ( ;-) ) with a more cleaner hash table, that might solve the problem with epn
-> all manual checks works (tried with root and non-root users)
-> nagios checks returns critical status with this output: "Service check did not exit properly"
I checked the Serial folder, was Ok! with all permissions granted (for testing purposes)
First Thank you for your contribution it will help me a lot at work.
Man, im heaving a hard time to use this
Manually it works perfect well as u can see it below:
OK: Fortigate Dinamica (Master: FGT80CXXXXXXXXX): IPSEC Tunnels: Configured/Active: 1/1 |'ActiveSSL-VPN'=0 'ActiveIPSEC'=1
I already declared the command at commands.cfg like this:
define command {
command_name check_fortigate_cpu
command_line $USER1$/check_fortigate.pl -H $HOSTADDRESS$ -C $ARG1$ -T cpu
}
and use the check like this
check_fortigate_cpu!public
but i receive this at nagios webportal
(Service check did not exit properly)
Do you have any ideias about how to fix this?
Thanks in advance.
Allan Lago
Hi allan,
did you run this plugin as root, if so permissions of FortiSerial path might be wrong?
Please check path: "/usr/lib/nagios/plugins/FortiSerial" (default path for storing serial information), in there should be a file with the ip of your device.
your plugin smells good ! Many thanks !
But when I try to implement the commands in Nagios, I got the following : "(Service check did not exit properly)"
When I launch the script manually, I got the following :
OK: (Master: XXXXXX) CPU is okay: noSuchObject%|'cpu'=noSuchObject%;80;90
Any idea please ?
Seb
Hi highfeeling,
sorry about this late comment, i didnt notice it.
It seems that you are using an older version of fortigate os, i've tested this script on FortiGate 100D / FortiGate 300C (both 5.0.3)
Greetings
Oliver


 New Listings
New Listings