Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
check Windows certificates health
Current Version
0.1
Last Release Date
2013-05-04
Compatible With
- Nagios 3.x
Owner
Website
License
GPL
Hits
49755
Files:
| File | Description |
|---|---|
| lotp_check_certificates.ps1.txt | lotp_check_certificates.ps1.txt |
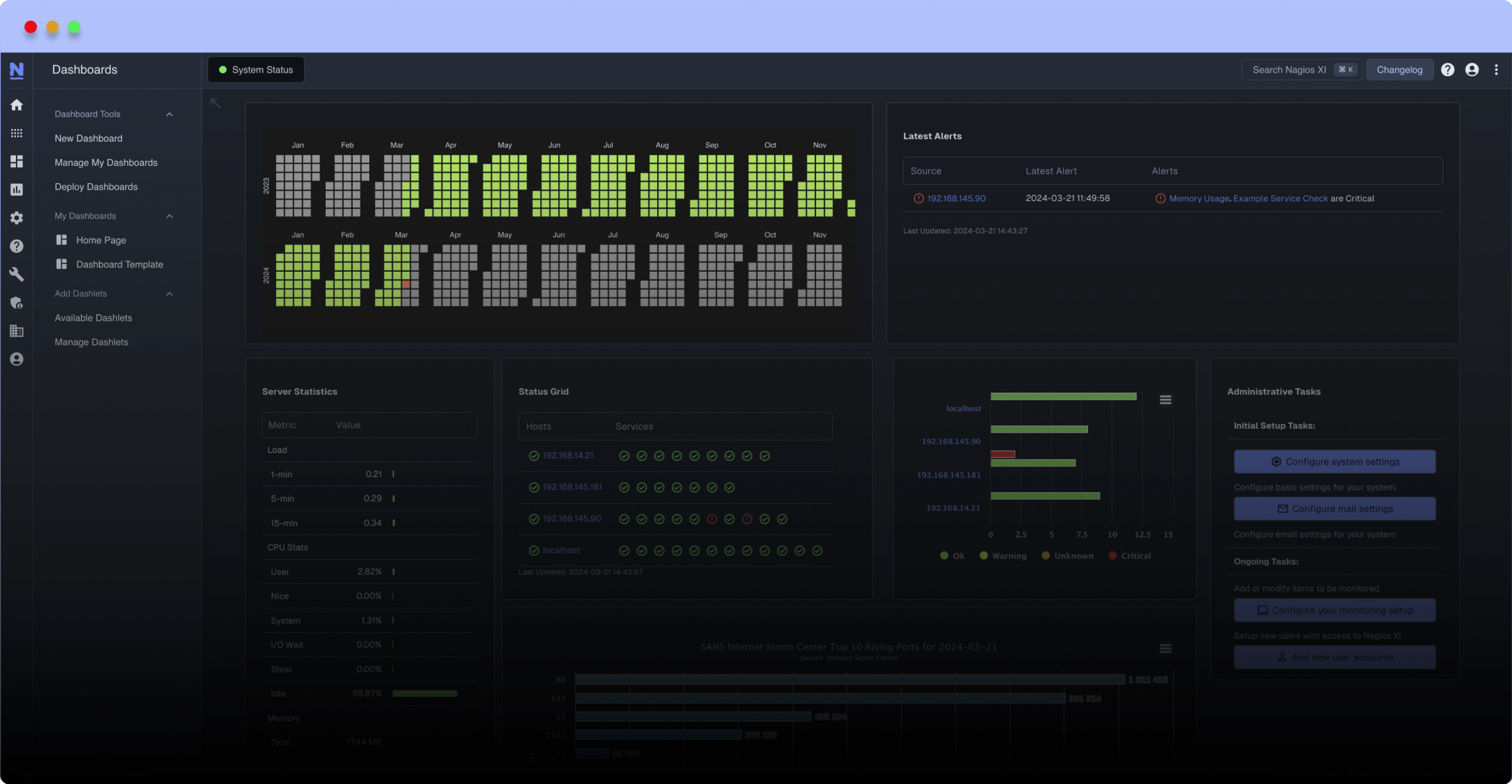
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
-My store (machine)
-Root store
-CA store
-Auth store
-SharePoint store
You can specify number of days before expiring, and threshold for warning / critical
All known already expired certificate in store, provided by Microsoft on all Windows Server 2003 / 2008 / 2012 are ignored
Check installed certificates in Windows store using powershell through NRPE / nsclient++:
-My store (machine)
-Root store
-CA store
-Auth store
-SharePoint store
You can specify number of days before expiring, and threshold for warning / critical
All known already expired certificate in store, provided by Microsoft on all Windows Server 2003 / 2008 / 2012 are ignored
###############################################
Tested Setup:
Monitoring Box:
-Centos 6.4 x64
-Nagios 3.4.4
-check_nrpe 2.13
-Centreon 2.4.2
-nsclient++ 0.4.1 x64 & x86
-Windows Server 2003 / 2008 R2 / 2012
-tested on both Core & GUI Servers
###############################################
Scripts arguments
The script accept eight arguments:
-checkMyStore (true by default)
-checkRootStore (true by default)
-checkCAStore (true by default)
-checkAuthRootStore (true by default)
-checkSharePointStore (true by default)
-expireInDays (60 by default)
-maxWarn (Warning if above)
-maxCrit (Critical if above)
###############################################
Local execution example:
PS C:Program FilesNSClient++scripts> . .lotp_check_certificates.ps1 $true $true $true $true $true 60 0 0
CRITICAL: *.mydomain.net:2013/06/05
PS C:Program FilesNSClient++scripts>
NRPE execution:
[root~]# /usr/lib64/nagios/plugins/check_nrpe -H myserver -n -c check_certificate -a $true $true $true $true $true 60 0 0
CRITICAL: *.mydomain.net:2013/06/05
[root~]#
###############################################
Installation:
On Windows Servers:
-copy script in folder C:Program FilesNSClient++scripts
-enable powershell script execution without signed : Set-ExecutionPolicy RemoteSigned
-Add to nsclient.ini:
[/settings/external scripts/wrapped scripts]
check_certificate=lotp_check_certificate.ps1 $ARG1$ $ARG2$ $ARG3$ $ARG4$ $ARG5$ $ARG6$ $ARG7$ $ARG8$
###############################################
Configuration:
For example, on Centreon:
-Add a new command:
$USER1$/check_nrpe -H $HOSTADDRESS$ -t 60 -n -c check_certificate -a $ARG1$ $ARG2$ $ARG3$ $ARG4$ $ARG5$ $ARG6$ $ARG7$ $ARG8$
Then add monitoring filling the ARGS. (using $$true and $false to escape correctly).
-My store (machine)
-Root store
-CA store
-Auth store
-SharePoint store
You can specify number of days before expiring, and threshold for warning / critical
All known already expired certificate in store, provided by Microsoft on all Windows Server 2003 / 2008 / 2012 are ignored
###############################################
Tested Setup:
Monitoring Box:
-Centos 6.4 x64
-Nagios 3.4.4
-check_nrpe 2.13
-Centreon 2.4.2
-nsclient++ 0.4.1 x64 & x86
-Windows Server 2003 / 2008 R2 / 2012
-tested on both Core & GUI Servers
###############################################
Scripts arguments
The script accept eight arguments:
-checkMyStore (true by default)
-checkRootStore (true by default)
-checkCAStore (true by default)
-checkAuthRootStore (true by default)
-checkSharePointStore (true by default)
-expireInDays (60 by default)
-maxWarn (Warning if above)
-maxCrit (Critical if above)
###############################################
Local execution example:
PS C:Program FilesNSClient++scripts> . .lotp_check_certificates.ps1 $true $true $true $true $true 60 0 0
CRITICAL: *.mydomain.net:2013/06/05
PS C:Program FilesNSClient++scripts>
NRPE execution:
[root~]# /usr/lib64/nagios/plugins/check_nrpe -H myserver -n -c check_certificate -a $true $true $true $true $true 60 0 0
CRITICAL: *.mydomain.net:2013/06/05
[root~]#
###############################################
Installation:
On Windows Servers:
-copy script in folder C:Program FilesNSClient++scripts
-enable powershell script execution without signed : Set-ExecutionPolicy RemoteSigned
-Add to nsclient.ini:
[/settings/external scripts/wrapped scripts]
check_certificate=lotp_check_certificate.ps1 $ARG1$ $ARG2$ $ARG3$ $ARG4$ $ARG5$ $ARG6$ $ARG7$ $ARG8$
###############################################
Configuration:
For example, on Centreon:
-Add a new command:
$USER1$/check_nrpe -H $HOSTADDRESS$ -t 60 -n -c check_certificate -a $ARG1$ $ARG2$ $ARG3$ $ARG4$ $ARG5$ $ARG6$ $ARG7$ $ARG8$
Then add monitoring filling the ARGS. (using $$true and $false to escape correctly).
Reviews (1)
byFlynJets, March 30, 2014
The -maxWarn & -maxCrit parameters aren't described well in my opinion. They are the number of certs that are expired or will expire. so -maxWarn 1 -maxCrit 2 will give you a warning if 1 cert will expire or a critical if 2 or more certs are expiring.
I'm more interested in setting the number of days ahead of expiration for my warning and critical alerts.
I'm more interested in setting the number of days ahead of expiration for my warning and critical alerts.


 New Listings
New Listings